-
I think i am more worried about breaking the warranty tag than taking a soldering iron to a new DSA
 Too bad there was not a software way to short pins 7/8
Too bad there was not a software way to short pins 7/8
Howard any more pics available of the inside of your dsa815 I think those of us with new machines will be staring at that warrant void sticker armed with your discovery and going for it
One thought on the dhcp thing If I want a fixed IP address ect what if i change to the fixed IP address that I want then perform your upgrade Will the default dhcp address be overwritten ontop of the manual address? just wondering
-
I think the example I'm familiar with has been apart enough for now! But if it's disassembled again I'll organise some new pics.
Not sure about whether the IP address fixes after shorting pins 7 & 8, I was happy to live with DHCP. You definitely cannot change network settings after the pin 7&8 short mod though. However, you can if you're brave enough to do the PIC mod.
Links by the way are here:
https://www.eevblog.com/forum/testgear/sniffing-the-rigol's-internal-i2c-bus/msg567821/#msg567821
https://www.eevblog.com/forum/testgear/sniffing-the-rigol's-internal-i2c-bus/msg572507/#msg572507
Here's a DaveCAD of that PIC mod BTW.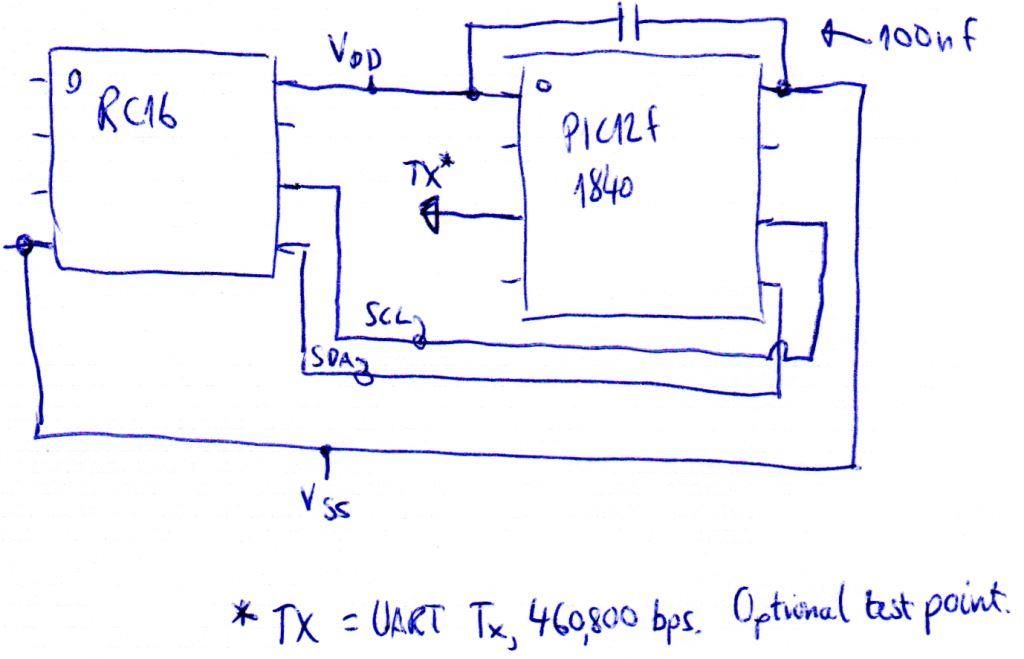
-
Hi!
Has anyone a dump from DSA815 Bootloader?
Thanks! -
Howard thanks
I am going to study up on how to remove the warranty void sticker and make sure I dont have a dissaster there. I think My skill level is more suited to Jumping pins 7,8 than the pic route. Thanks for all that you and the rest have done ! While the lower RBW would be great and may get "hacked" on the 1.04 bootloader some day, folks like you who take the chance to help the rest are Appreciated.
big thanks from Boston, Ma -
Hello all, damn I wish I would have had the $$$ and purchased the DSA815-TG before they came out with this last rev that wont allow any of the hacks to work! Now am debating whether or not to install the latest firmware or wait hoping the hack gurus will come come up with a fix ?
Is anyone looking into a fix for the 815 ?
73 N8AUM -
Hi
first of all I'd like to thank everyone here for their great work.
I have a small problem with my MSO1074Z. I dumped the 64M image using my PI and generated the license codes using the rigup-0.4.1 tool posted in #7323 (https://www.eevblog.com/forum/testgear/sniffing-the-rigol%27s-internal-i2c-bus/msg565557/#msg565557). I had no errors during this process. I can confirm that the serial number in the TXT file (after the scan command) is the same as display by the device itself. I tried to enter the generated codes for 0x1C00F and 0x1C001, but had no luck. The MSO always responds: "Invalid license".
I was so frustrated that I pushed the apply-button a little bit too often. Now I have to wait at least 12h before I can continue.
What did I wrong? Is the firmware too old? My firmware version is 00.04.00. To which version should I upgrade? Do I have to redump the image again after the upgrade?
Many thanks in advance.
Juergen
-
Hi
I have upgraded to 00.04.02.SP4 and tried to reenter the already obtained codes. It still fails. Do I have to re-dump the binary again in order to get new(??) keys?
Regards
Juergen
PS: The scope is only a few hours old. The trail versions are still going. Could this be an issue? -
Hi guys,
I figured it out... I initially compiled it on my OSX machine. As I switched to Ubuntu the keys changed and now everything works fine.
I so far only applied 0x1C00F and 0x1C080. Those are missing:
(CSAS = 0x1C010) DG
(CSRA = 0x1C020) 500uV
(CSBA = 0x1C040) Power Ana.
As I understand 500uV is useless (see #3731), but what about the other 2? What are they for? Are they "harmful" (as noted here #3723)??
Regards,
Juergen
-
What chances are there to patch a firmware so that it outputs the key and serial when you send it
"*IDN?". That would be good.
Done!
https://mega.co.nz/#!MdcEWTgL!0EEmSr-Q6TxaFSsyEmjhRrgqDvFCoXg9K49BalL5Uxc
No need for JTAG memory dumps anymore, just send *IDN? command and you'll get your license encryption keys in response (tested on my DS2072A that has just arrived).
This file is no longer available. Can someone please direct me to the file?
Thanks. -
Hello Guys,
Just a message to report another MSO1074Z unlocked
Thank you to all the people contributing with their knowledge, effort, time, energy ... It's good to know that sharing is a good path to success.
Special thanks to rmd79, 0ff, Hammy, Howardlong and the guys who discovered and shared the hack in the first place sptm14, Slappy_g and for sure all the others I'm forgetting ... sorry, the thread is very long and many have contributed.
For those interested this is how I did it:
- First I tried with an Olimex JTAG header but neither Windows (7 32-bits), nor MAC OS X (Yosemite), nor Linux recognised it.
- I decided to try with the Bus Pirate V3.6 (BP) from Dangerous Prototypes and this worked at the first try (I think I got a defective Olimex ).
).
- I did the memory dump using Linux (only because I was doing something in that machine and decided to try the BP, but I think it would have worked with the MAC as well, I did't tried).
- I used openocd and the result was a binary file of 67108863 Bytes.
- I used the updated version of rigup tool that takes into account the MSO1074Z and get the private key
- I used again rigup tool and generate the licenses
- I used the SCPI commands to enter the licenses and voila !!
The only thing I can contribute with since I haven't seen it here, is the use of the BP (Bus Pirate), the rest is according to the information given in the forum, so here it goes:
If someone is interested this guide was really helpful in putting Bus Pirate to work with openocd (under linux):
http://cybermashup.com/2014/05/01/jtag-debugging-made-easy-with-bus-pirate-and-openocd/
First a little disclaimer: This interface is really slow, when the guys from Dangerous Prototypes say that this is a human speed tool they are not kidding, it took several hours (25+) to get the dump done.
The cabling was pretty straight forward:
Oscilloscope BusPirate
TDO <------------> MISO (According to the label in the PCB, however when in JTAG mode it is TDO as it is supposed to be)
TCK <------------> CLK (Again in JTAG mode this is TCK)
TMS <------------> CS (Which is TMS in JTAG mode)
TDI <------------> MOSI (TDI in JTAG mode)
3.3V <-----------> 3.3V
GND <-----------> GND
I didn't use the other pins.
The openocd command line:
user@system:/home/user#openocd -f mybuspirate.cfg
File: mybuspirate.cfgCode: [Select]
source [find interface/buspirate.cfg]
source [find target/imx28cfg]
buspirate_mode normal
buspirate_pullup 0
buspirate_speed fast
buspirate_port /dev/ttyUSB0
/!\ The port where the Bus Pirate was detected in my computer was /dev/ttyUSB0, you must change the previous line according to whatever it is in your case!
once the interface was reporting this:
Info : Buspirate Interface ready!
Info : This adapter does not support configurable speed
Info : JTAG tap: imx28.cpu tap/device found: 0x079264f3 (mfg: 0x279 part: 0x7926, ver: 0x0)
Info : Embedded ICE version 6
Info : imx28.cpu: hardware has two breakpoint/watchpoint units
Info : Accepting 'telnet' connection on tcp/4444
I did the telnet to tcp port 4444Code: [Select]user@system:/home/user#telnet localhost 4444
Trying 127.0.0.1...
Connected to localhost.
Escape character is '^]'.
Open On-Chip Debugger
> halt
target state: halted
target halted in ARM state due to debug-request, current mode: Supervisor
cpsr: 0x40000013 pc: 0x401e1104
MMU: enabled, D-Cache: enabled, I-Cache: enabled
> dump_image mso1074z.bin 0x40000000 0x3FFFFFF
dumped 67108863 bytes in 91906.320312s (0.713 KiB/s)
target state: halted
target halted in ARM state due to debug-request, current mode: IRQ
cpsr: 0x40000092 pc: 0x001c17a0
MMU: enabled, D-Cache: enabled, I-Cache: enabled
Then I ran the rigup tool with the dump file as parameterCode: [Select]user@system:/home/user#./rigup scan mso1074z.bin > mso1074z.txt
which generated the private key/public key/RC5 keys/Serial Number
After with the latter file I ran again the rigup tool to generate the licenses:Code: [Select]user@system:/home/user#./rigup license mso1074z.txt 0x1C001
or as Sandra suggested in her post "Reply #3765" page 252 of this thread
This is a summary of the found options as far as I know:
(CSAR = 0x1C001) TRIGGER --> Applied
(CSAB = 0x1C002) DECODER --> Applied
(CSA3 = 0x1C004) MEM-DEPTH --> Applied
(CSAJ = 0x1C008) RECORDER --> Applied
(CSAS = 0x1C010) DG --> Not clear yet on what this option does
(CSRA = 0x1C020) 500uV --> Reported not to work correctly
(CSBA = 0x1C040) Power Ana. --> Not clear yet on what this option does
(CS3A = 0x1C080) Bandwidth (100MHz) --> Applied
(CSHY = 0x1C0FF) --> Kind of APPLY ALL!
And finally to apply the generated licences the easiest way is to use the scope's SCPI interface:
Configure the LAN interface of the MSO1074Z:Code: [Select]Utility —> IO Setting —> LAN Conf.
You can connect the scope through a switch or back to back to your PC in any case this is the setup:
[Oscilloscope] --- straight Cable -----[Switch] ------ straight Cable ------- [PC]
or
[Oscilloscope] ------------- Crossed Cable ---------------- [PC]Code: [Select]user@system:/home/user#telnet <Oscilloscope LAN IP Address> 5555
:SYSTem:OPTion:INSTall <The Activation Code WITHOUT the dashes or spaces>
I hope this will help someone, I tried to complete with some information that was spread in several posts; if you want to see some pictures go to Sandra's post which have some very useful ones (notably for the Oscilloscope JTAG interface).
Cheers,
Gus -
Congrats pherseus!

25+ hours dump with the BusPirate



-
Thank you Hammy,
Actually, to be fair I think the BP is not that slow, what happened was that after some hours (8+) my computer went to sleep and the dump just stopped, the day after I thought the dump was finished because the USB led in the BP was not blinking, but when I woke up the computer the USB led got blinking again.
Anyway it was really slow,
Cheers,
Gus -
Could we use this latest meathod on the dsa815, or is the unit and or keygen sufficiently different that it wont work.
-
I did try it on a RAM dump, but I couldn't get it to work, it wouldn't find a key, but I am no expert at this level.
-
Could I get a quick recommendation for a Jtag that will work with one of the guides in this thread, and might be good to use for other things later? Preferably one that I won't have to fight with to get it working.
Thank you in advance for the answer. Sorry for not digging through the thread. -
New Firmware for DS1000Z and MSO/DS2000 Here
Do these updates on the MSO1000Z series interfere with the JTAG hack? -
New Firmware for DS1000Z and MSO/DS2000 Here
Do these updates on the MSO1000Z series interfere with the JTAG hack?
Nope. -
Hello All!!
Yet not working,
I make the dump, problem was excessive length of cable.
Then the new released rigup 0.4.1 modified for MSO1000Z generate the keys and license codes, no problem.
I compiled rigup under Ubuntu, only problem a linker warning and core dump with -dead-strip option.
After I remove this option it compiles and work well.
The license codes does not work. The oscilloscope claim "invalid license" all the time.
I try to enter codes both via SCPI and keyboard with not luck.
I don't know were is the problem..
Perhaps can be a problem during program build... I see some warnings..
Can Someone send me the ubuntu 64 bits binary for rigup program to test is against mine for key generation??
Please send me personal message.
Thank You!
Regards
Manuel -
Any news on the DG4000 series after v1.09?
(Edit on advice of Teneyes...)
After forgetting to revert to DG4162 from DG4202 before update, I'm stuck with DG4062 at v1.10. Is there any hope? -
Hey!!
My MSO1074Z-S got now all options Official!!
I managed to discover the problem..
In the new version of rigup, When I use "rigup serial keys.txt MSZ..." to update the serial number, it solves the problem....
Then some of preinstalled licenses with rigup search test Ok. Previously they test Fail.
Then I regenerate the licenses and now they test also Ok with "rigup info" command.. Previously they test Fail.
Also i update the firmware after apply licenses and no problem.
Thank You All, specially to users smgvbest for her tutorial at page 252 and to rmd79 for the rigup application.
Regards
Manuel -
After forgetting to revert to DG4162 from DG4202 before update, I'm stuck with DG4062 at v1.12. Is there any hope?
Perhaps you mean DG4062 with v01.10? There is no v01.12 for DG4000 series yet. -
Hey!!
My MSO1074Z-S got now all options Official!!
Regards
Manuel
Glad you got it
-
Yeah, I got a license OFFICIAL for my MSO1074z
 !
!
I used Olimex adapter https://www.olimex.com/Products/ARM/JTAG/ARM-USB-TINY/ , but it is not connected to the scope port I do not know why, probably there is a problem with the drivers Windows 7 and Linux (Ubuntu x64).
I do not know why, probably there is a problem with the drivers Windows 7 and Linux (Ubuntu x64).
I asked at the local forum another adapter from a friend. It was a cheap Chinese Segger J-link adapter for $ 20
Next I used https://www.segger.com/jlink-software.html?step=1&file=JLink_496d to communicate with the "segger" adapter.
To dump commands are used Halt "h" and "savebin" commands. I also increased the speed of the bus to 6MHz ("speed 6000" command). The 64 MB memory dump copied 8 minutes.
Then I used rigup 0.4.1 under Debian Linux i386, but I changed the Makefile "LDFLAGS: = -O2 -Wl, - gc-sections c" as written here on the forum.
Rigup generated correct keys for my scope
Thank you ALL !!! -
Do any of you folks this will work with the DSA815tg's ?
-
Here's part of the source code in riglol.c (source code can be downloaded at the bottom of http://riglol.3owl.com)
I don't know who wrote/maintains this code, but I found a small bug that I want to report.
There is a line which may or may not function as desired depending on the compiler.
Here is my simple fix:Code: [Select]--- riglol_orig.c 2015-02-03 12:53:18.659248144 -0800
+++ riglol.c 2015-02-03 12:54:16.283267920 -0800
@@ -141,7 +141,7 @@
char * strtoupper(char *str) {
char *newstr, *p;
p = newstr = (char*) strdup((char*)str);
- while ((*p++ = toupper(*p)));
+ while (*p = toupper(*p)) { p++; }
return newstr;
}