Cerebus has a little script that will generate a random email address, installs an alias for it and a note of what it was generated for on his mail server and spits out a random password. Cerebus then just cuts and pastes the email address and password into whatever site needed a new credential and leaves the rest to Cerebus' password manager. Thus no two sites share credentials and when the inevitable spam arrives, Cerebus knows who leaked his details, often before the news gets out publicly that such-and-such a site has been hacked and leaked n million credentials into the wild.
Good good. 2FA is still good because it kills keyloggers dead as you need a physical device external to the machine (phone / TOTP key etc). My father-in-law had his Halifax account emptied after someone keylogged his login details.
There have been successful attacks on bank accounts "protected" by using a phone as 2FA

Once they have your banking login/password, the mechanism is:
- your mobile phone number, stored/leaked from some other site, becomes known to the malefactors
- the malefactors contact the phone company and move the phone number to a SIM in their phone. SOP for the mobilr phone company, of course
- all 2FA stuff now goes to them
The only defense against that which I can see is to have a second mobile phone used
only for banking.
Bit of a pain if you then need to carry two phones around, and you need to remember to use that phone occasionally to stop the number being recycled.
Check your eBay accounts for signs of hacking, woke this morning to discover a string of emails from eBay informing me that I had successfully added 2 stage verification to my account at 03:01 precisely, strange because I was in bed asleep then, and then proceeded to add 4 exercise bikes all priced in Euro's, yeah right, they can feck right off.
Onto eBay chat and all sorted, account re secured and bogus items removed from my listings, thanks eBay for a quick resolution. 
Was it an issue with the two stage verification or lack of? I haven't 'upgraded' mine as two stage logins on Ali Express are already giving me the sh1T's
Same here... I've actually got a bit of a PTSD reaction after multiple arguments with that BS system.

bad enough that when I think about shopping there for something I know I should be able to get cheap, half the time I say
"Fukkitt!!!" and just order off Amazon.

Of course, same has been true of fleaBay & Bang-em-good for a while now... I have several thousand BG affiliate points I haven't spent because every time I find something I actually WANT, it isn't eligible because it's on some fucking promotion or other.

mnem
Sometimes you have to just chuck it in the Fukkitt Bucket and get on with your life.
Cerebus has a little script that will generate a random email address, installs an alias for it and a note of what it was generated for on his mail server and spits out a random password. Cerebus then just cuts and pastes the email address and password into whatever site needed a new credential and leaves the rest to Cerebus' password manager. Thus no two sites share credentials and when the inevitable spam arrives, Cerebus knows who leaked his details, often before the news gets out publicly that such-and-such a site has been hacked and leaked n million credentials into the wild.
I do the same, but manually. How do you automatically generate an alias? BTW Don't you have a max number of alias for your domain?
I am worried to hit the max alias number limit one day.
That spider is why they invented fire
Cerebus has a little script that will generate a random email address, installs an alias for it and a note of what it was generated for on his mail server and spits out a random password. Cerebus then just cuts and pastes the email address and password into whatever site needed a new credential and leaves the rest to Cerebus' password manager. Thus no two sites share credentials and when the inevitable spam arrives, Cerebus knows who leaked his details, often before the news gets out publicly that such-and-such a site has been hacked and leaked n million credentials into the wild.
Another technique is based on gmail's interpretation of what's in front of the "@". foo@gmail.com is exactly the same as foo+eevblog@gmail.com, since anything after the "+" is ignored. I've caught one company out that way. Plus "." is ignored so foo@gmail.com and f.o.o@gmail.com are the same account.
The downside, which I'm currently experiencing with the IET, is organisations that don't allow a "+" in the address you give them to use to contact you.
For reference, all these are valid email addresses:
Ælfred+þor@gmail.com
Abc\@def@example.com
Fred\ Bloggs@example.com
Joe.\\Blow@example.com
"Abc@def"@example.com
"Fred Bloggs"@example.com
customer/department=shipping@example.com
$A12345@example.com
!def!xyz%abc@example.com
_somename@example.com
Ahh yes the wanton disrespect of RFC email addresses across the internet buggers that up. I do a Cerebus and I’ve got an email alias for each account I create. It’s all in keepass so I don’t give a crap

. I use the last 8 characters from a GUID for each one. Not automated as it wasn’t worth it.
Still trying to not buy an IC-7300. Come on people you are enablers. Do your jobs!
The flip side to that scheme is that it's relatively easy to guess what the 'add part' is and so if a malicious party has obtained a legitimate 'base part' it's trivial for them to automate trying alternative 'add parts' on the most lucrative targets to find a valid combination by brute force. The random user part is impractical to brute force (the scheme I use has ~ 44 bits of entropy) but requires you to have access to a mail server where you can add as many user parts as you like to an email domain without (significant) additional costs to oneself.
Although all the above is true, I don't regard it as a significant weakness in your scheme. I tend myself to regard the random email address as 'security by obscurity' and really use it for the purposes of 'traitor tracing'. It's having a unique, random password per site that gives me some comfort. As you say, broken implementations that don't follow RFC822 et seq are the pain point for your scheme, and they are, from experience, so common that it's a serious drawback.
Yes. The reason it never works is almost always some numpty copied a regular expression off stack overflow that worked on the two email addresses they tried it on. That’s literally it. It’s pretty easy to write a simple recursive descent parser that pukes on an unexpected token

. It’s actually fun doing that.
I’m only interested in traitor tracing as you so elegantly put it.
The flip side to that scheme is that it's relatively easy to guess what the 'add part' is and so if a malicious party has obtained a legitimate 'base part' it's trivial for them to automate trying alternative 'add parts' on the most lucrative targets to find a valid combination by brute force. The random user part is impractical to brute force (the scheme I use has ~ 44 bits of entropy) but requires you to have access to a mail server where you can add as many user parts as you like to an email domain without (significant) additional costs to oneself.
Although all the above is true, I don't regard it as a significant weakness in your scheme. I tend myself to regard the random email address as 'security by obscurity' and really use it for the purposes of 'traitor tracing'. It's having a unique, random password per site that gives me some comfort. As you say, broken implementations that don't follow RFC822 et seq are the pain point for your scheme, and they are, from experience, so common that it's a serious drawback.
All valid.
The objective is to nail the leak, no more.
The reason it never works is almost always some numpty copied a regular expression off stack overflow that worked on the two email addresses they tried it on. That’s literally it.
They probably couldn't figure out how to use '+' as a token instead of as an operator.

The reason it never works is almost always some numpty copied a regular expression off stack overflow that worked on the two email addresses they tried it on. That’s literally it.
They probably couldn't figure out how to use '+' as a token instead of as an operator. 
I have a low opinion of stackoverflow, except for "which button do I press to mangle the wurzel" questions. And the answers usually have all the depth of ctrl-A ctrl-C ctrl-V.
Hence it would surprise me if they understood the concepts of "operator" and "token".
I have washed it with windows cleaning fluid

the both bulbs are interesting
the both bulbs are interesting
Indeed, additional winter lab heating.

the both bulbs are interesting
Indeed, additional winter lab heating. 
Watch out with those black metal tubes, it could be the anode (Yes, personal experience

)
Martin.M I admire when you start a project you seem to close it in a short time.
I have tons of projects open and I do not know when I will end them...

Thanks for posting here, amazing!
the both bulbs are interesting
Indeed, additional winter lab heating. 
Watch out with those black metal tubes, it could be the anode (Yes, personal experience  )
)
Not an issue with those 6SH7's. No connection to the metal shell.
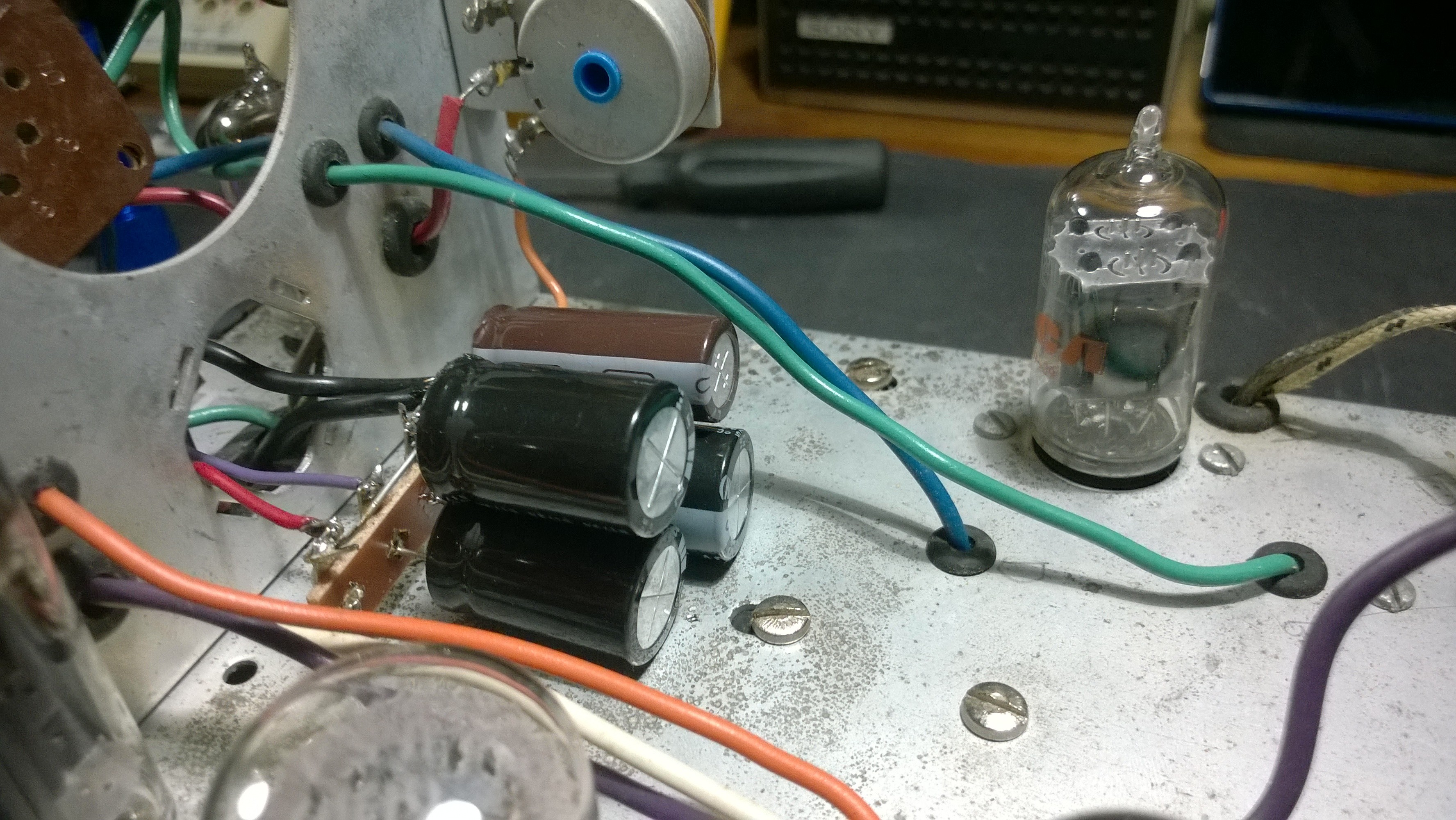
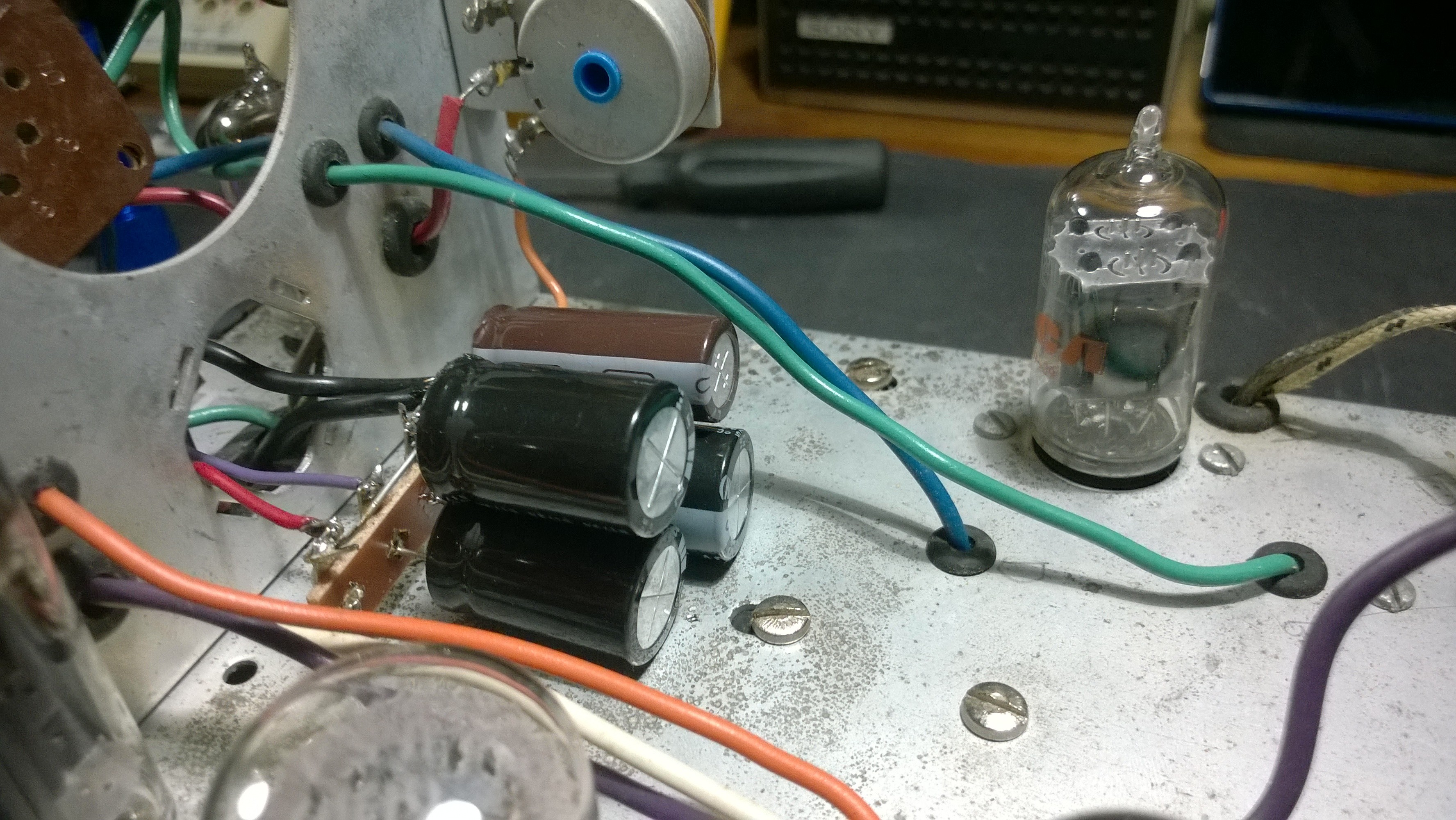
Finally received the capacitors for the RCA 54-45 Scope. Here's the new B+ filter capacitors installed on the terminal strip. 1- 47uf/450v and 3- 22uf/450V. This replaces the original 4 section metal can. After that was complete re-installed the CRT.
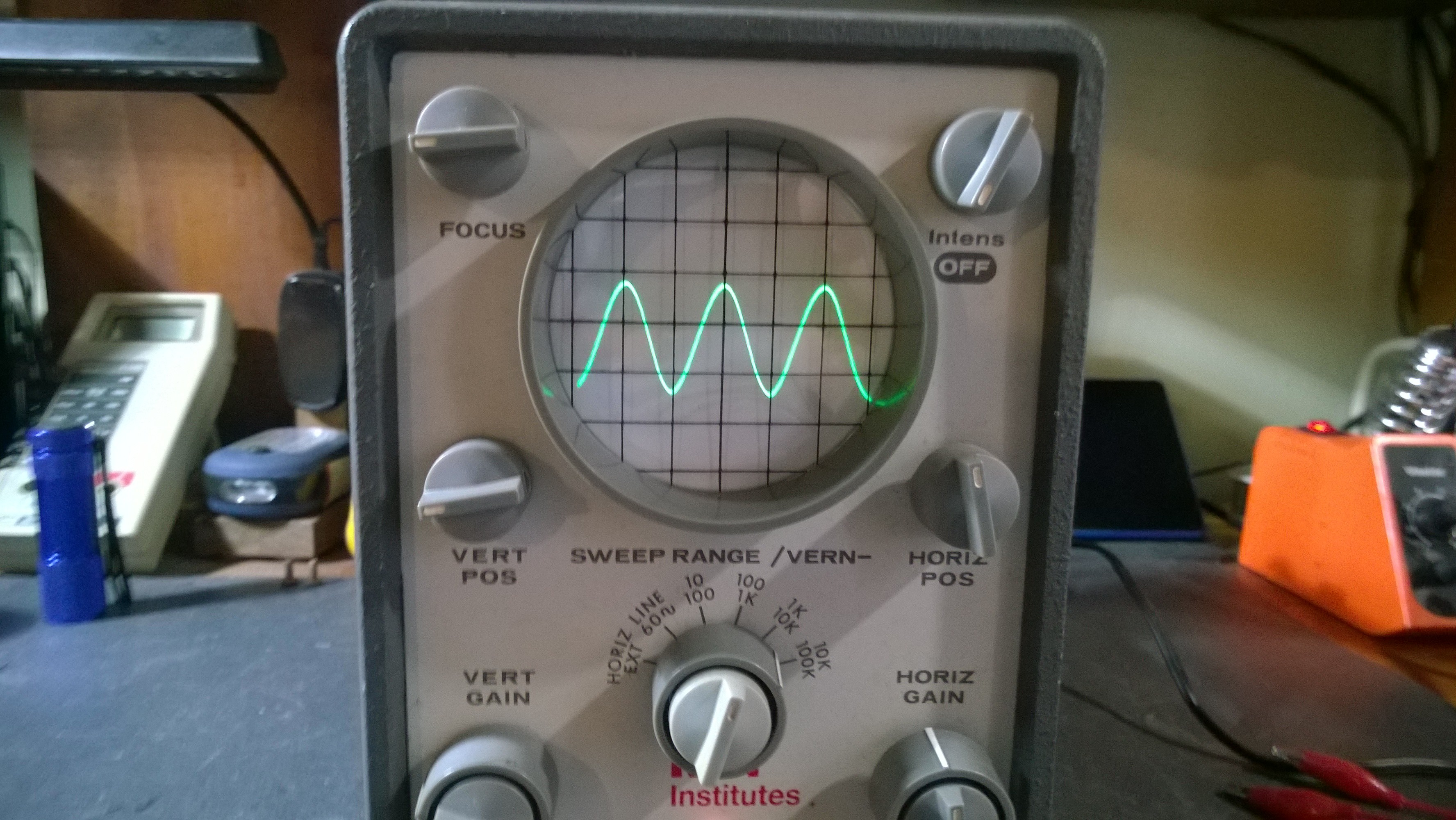
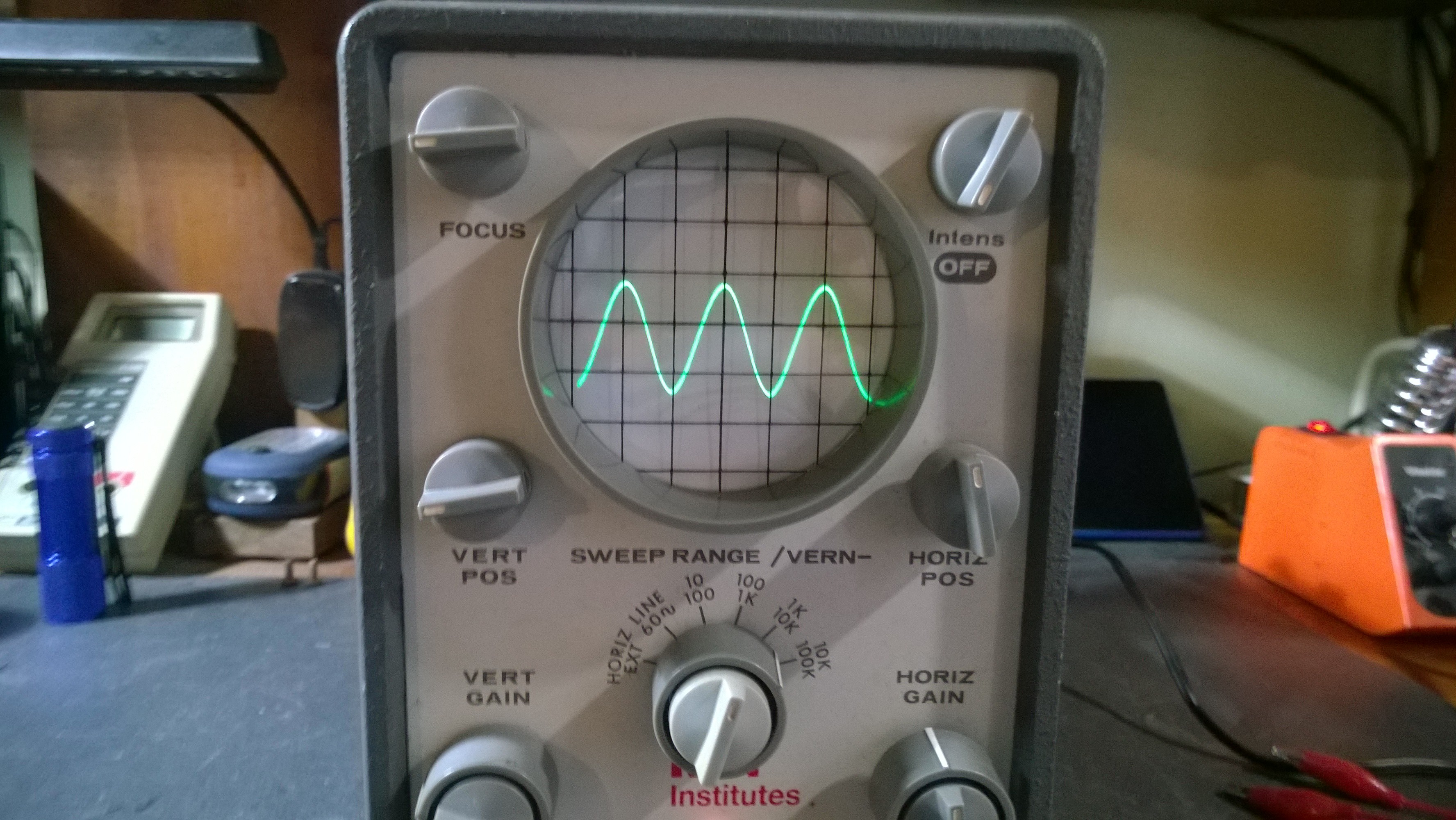
Replaced 1 -50uf/10V cap in the vertical pre-amp and decided to give the scope a test before going any further. All I can say is "Wow".

The trace is now sharp and stable. The B+ can was definitely defective. And I still have to replace the caps in the Horizontal/Sync section and the HV caps. But this guy is looking great as is. And at this point I don't see the need to perform the OA2 VR mod.
Tomorrow I'll replace the balance of the capacitors and then this one should be done.









 bad enough that when I think about shopping there for something I know I should be able to get cheap, half the time I say "Fukkitt!!!" and just order off Amazon.
bad enough that when I think about shopping there for something I know I should be able to get cheap, half the time I say "Fukkitt!!!" and just order off Amazon. 

Pommie stirring TEA defenses ENGAGED
 Cute little one and I will migrate it tomorrow to the garden.
Cute little one and I will migrate it tomorrow to the garden.

 . I use the last 8 characters from a GUID for each one. Not automated as it wasn’t worth it.
. I use the last 8 characters from a GUID for each one. Not automated as it wasn’t worth it.  . It’s actually fun doing that.
. It’s actually fun doing that. 








 )
)


 )
)
 The trace is now sharp and stable. The B+ can was definitely defective. And I still have to replace the caps in the Horizontal/Sync section and the HV caps. But this guy is looking great as is. And at this point I don't see the need to perform the OA2 VR mod.
The trace is now sharp and stable. The B+ can was definitely defective. And I still have to replace the caps in the Horizontal/Sync section and the HV caps. But this guy is looking great as is. And at this point I don't see the need to perform the OA2 VR mod.